
![]()
Created May 12, 1994 - Last modified on Monday, April 6, 2020.
Latest changes in blue!!

![]()
Created May 12, 1994 - Last modified on Monday, April 6, 2020.
Latest changes in blue!!
The following represents a huge amount of work on my part that I have brought together because I care. Please feel free to read, understand, and refer others, but I do claim © copyright on all of it and request that you get my written permission before making copies for any use. This has become an evolving source of information. Please email me with any criticism and or suggestions. Thank you. Bill
I built a PC for a savvy host computer guru who knows little about PCs. He was really pleased at how well his PC worked with it flying compared to his early IBM PC clone. After six months he brought back this PC barely running. He could not understand why it went from working so wonderful to just plain terrible. The problem was he just did not understand the key to system performance is in the hands of the PC user. Knowing some fairly simple things will avoid a lot of frustration and help keep your PC working efficiently. Frankly, I have been buried by friends and clients with similar problems, so decided to prepare these web pages to improve PC understanding and avoid similar problems.
I consistently see the same ignorance caused problems with backups, drivers, garbage files, and automatic applications. People get so used to their PCs being reliable that they fail to regularly back up then get burned badly when the inevitable hardware failure occurs. They also tend to load lots of programs without being aware they are also reloading driver files that are often incompatible with their sound, video, printing, and even disk drives. Finally, most, particularly Internet users, tend to let their storage and memory fill up until their PC will not work. We get more and more things running and everything runs slow. It only takes a few minutes to understand what causes these problems and what you need to do to avoid them.
First, you should know that depending upon the kind of system you have, what you will need to do is different. When I first wrote this guide, PCs used large eight-inch floppy drives with very few having small hard drives because a five-million-character hard disc cost over $100,000 in today’s 2020 dollars. Information was exchanged on floppy drives. Only those associated with the military and universities had access to the Internet. The Internet was almost exclusively text because the time to transmit a single picture was crazy. Communications evolved from modems that only transmitted data at thirty characters a second so it could take up to an hour to send a single picture. Now, most Internet providers supporting at least thirty thousand characters per second with some of the light fiber Internet providers now giving many hundreds of millions of characters per second. PCs also evolved. The total storage capacity of those early PCs would not even handle one single picture and they ran so slow even simple actions often took hours. Most today have PCs with hard drives and CDs with considerable capacity. Those with the latest PCs have a solid-state drive that has a quarter to a trillion or terabyte which equals 1000 billion characters of storage. Most of these high-end PCs come preloaded and don’t even offer a hard drive or CD drive except as addons you plug into separate ports.
Sadly, two things happened to me personally that showed my best backup efforts which most still teach were just plain bad. Unlike most others I have over fifty years large computer experience, so was very diligent about backing up my computer. I thought I was doing all correctly. What happened made me totally rethink how I did my own backups. Before sharing, please understand that my desktop contains a good portion of my life’s work. It contains my programs and engineering tools for my air quality and dust collection work. It contains all of the tools to maintain more than two-hundred web pages. It contains all of my materials for more than a dozen different engineering and computer science courses. It contains my presentations I give all over the world. It also contains my information library built up over twenty years responding to air quality and dust collection questions, plus the best expertise from all over the world. I pay an email service that gets rid of the spam and garbage pulling my daily email volume from over 6,000 a day to around 200 that I actually see. My library is vital to provide thorough responses as it allows me to respond to all in about four hours a day rather than spend over twenty. I am unwilling to lose this knowledge data base or go back to those brutal hours, so take extreme efforts to ensure all is very well backed up and I can resume work with a minimum disruption.
So, two things hammered me back to back that really educated me about how to do proper backups and restores. First, it was raining so hard the gutters could not keep up. In over fifty years of living in this area I had never seen such hard rainfall with so much water falling so quickly. My neighborhood has excellent grading and drainage, but our drains could not keep up and we had water that was up to three feet deep in the streets. My own yard and home is raised about four feet above the street, has good grading, plus I have large extra drains to carry excess water from the back yard to the street. The water from our backyard could not drain fast enough. We had water creep inside the home on two flooded walls from sill boards leaking. We were watching all close knowing just one more downpour and our home was going to become another in the huge number flooded by that unusual storm. While busy watching for that flooding, we were blindsided. A plastic pipe fitting in the ceiling above the first story of our home cracked. Most of the water poured down behind our kitchen appliances and the only initial symptom was a tiny drip in the upper corner of our refrigerator. We thought we had a roof leak as there was no water supply in that area. Then that pipe fitting burst and water cascaded everywhere flooding the ceiling above the kitchen, running down the walls, soaking all the appliances, flooding our kitchen, family room, dining room, entry way, pantry, etc. I got all turned off and paid to have the broken pipe capped so we could get the water back on, but our downstairs had flooded. We had to do an emergency move while it was still pouring outside to move all from the downstairs of our home into storage. Much of that stuff got put into the huge storage locker we rented wet. Our things were packed floor to ceiling for the whole dept of that unit. My PC was fine, but the backups went into storage. There was no way at all I could get access to those backup hard drives without pulling all out and unpacking the boxes our large team of movers packed until I found those drives. Worse, since all went in wet, much had molded and I have respiratory issues, so could not risk even trying to do that unpacking without wearing a full HEPA filtered respirator. My master bedroom, office and PC were upstairs, so I was able to keep living and working in my home while repairs were done downstairs. Unwilling to risk a PC disaster, I bought four extra hard drives, used one for incremental backups and the other three for full clone backups then disaster struck.
The second disaster was ugly as it cost me almost all of my PC programs, work and email from September 2014 through most of 2015 while our home was being repaired. Sometime in the past my PC caught a time-bomb type virus. It infected my computer then did nothing getting copied onto my clone backups which I did for nearly a year. Then on a particular date, mine and thousands of PCs all over the world had that virus timer go off. The virus waited until there had been no activity meaning typing on our computers for at least an hour, then it wiped all attached hard drives clean. I then only had the main hard drive and incremental hard drive attached. I had not yet added my solid-state drive.
I did my restoration stupidly. I reloaded my backup and all worked perfectly until I tried to reload my incremental backup files which were gone. I tried all kinds of tricks to restore those incremental files, but the virus had not only erased them, it had rewritten the hard disc in cascading patterns of ones and zeros leaving nothing to be found. Worse, after I had been away from the computer for a bit this virus again wiped all including that backup drive which I had left installed. That left me convinced I had a virus on my system, so I reloaded all again from an older backup, updated and ran my virus checker. Turned out when activated that virus blocked the updates to my virus checker which would have gotten rid of the virus.
With all wiped out again and only one backup remaining, I then called the Symantec help line as they are my antivirus and backup program provider. They acknowledged there was a nasty time-bomb type virus going around and told me the manual steps I could take to remove it. I had to rebuild my system from my memory stick, then reload the Symantec programs, go through their update process and then put in my older backup to check it for this virus. That virus was found on my backup and some of my operating system files. I clicked Ok to remove it from each instance not realizing that removal would wipe both my infected operating system and email files forever. My PC lost all my email and no longer ran after following their recommended steps. I called again, was told it was going to take a few weeks to get a full automated repair in place. They gave me a patch that kept the virus from working, but it still infected my computer.
I lost all my email and other files from before this virus struck. Most of my expensive computer programs were gone and could not be restored because I did not have all the information or rights to download a replacement copy. The only way I could have recovered these was from my full clone backups which that virus wiped out. My email was even worse, as I lost all past emails. My only salvation through all of that mess was after our stuff came out of storage, I was able to use the latest Symantec Norton antivirus to clean another earlier cloned backup drive, then was able to use it and add the incremental updates that I had built up. That let me only lose most of my downloaded programs and just about all of my email from 9/11/14 to 6/15 when that virus went off. Fortunately, I was also able to download the most current versions from my Internet pages.
Remember it is not just the cost of the equipment or programs at risk, but also your lost time and revenues. The odds are 100% that you will eventually have a major PC failure losing all unless you have proper backups. I have never forgotten a sticker I found inside my early Wang word processor system. It said, "This device is equipped with a psychic circuit that will detect the worst possible moment then fail!"
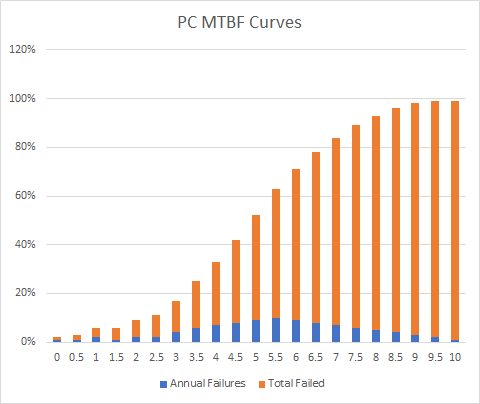 PCs are constantly improving where they last longer. Still, even newer PCs rely on complex electronic, electromechanical, and magnetic components that each have limited life cycles. Engineers test and share the MTBF which means the average (mean) time before failure for each part. For most parts product life is a bathtub shaped curve where there is an initial failure rate, then the rate of failure remains small and steady for the working life of the product, then things fail rapidly. In 1972 when I built my first PC parts reliability was often measured in days, but pretesting to remove initial failures and reliability improvements now in 2020 make most parts last five years before a catastrophic failure. Here is a graph to the right that in blue shows what percentage of PCs fail every year of life and in orange shows the accumulated PC failures over a ten-year period. Clearly, not only does this graph show your PC will fail, it shows you have about a one in three chance it will fail in three years, an even chance if will fail by five years and then all gets much worse from there. If your main storage fails, all is lost except what you have backed up.
PCs are constantly improving where they last longer. Still, even newer PCs rely on complex electronic, electromechanical, and magnetic components that each have limited life cycles. Engineers test and share the MTBF which means the average (mean) time before failure for each part. For most parts product life is a bathtub shaped curve where there is an initial failure rate, then the rate of failure remains small and steady for the working life of the product, then things fail rapidly. In 1972 when I built my first PC parts reliability was often measured in days, but pretesting to remove initial failures and reliability improvements now in 2020 make most parts last five years before a catastrophic failure. Here is a graph to the right that in blue shows what percentage of PCs fail every year of life and in orange shows the accumulated PC failures over a ten-year period. Clearly, not only does this graph show your PC will fail, it shows you have about a one in three chance it will fail in three years, an even chance if will fail by five years and then all gets much worse from there. If your main storage fails, all is lost except what you have backed up.
This is why most experts recommend you provide a full backups, incremental backups, and cloned backups. A full backup makes a copy of all the files on your PC allowing you to replace any that get lost, deleted, or compromised. For instance, should you lose all your email due to being hacked or your PC getting a virus, the full backup would let you restore your email file. Doing so means that you lose all changes that occurred after that backup was created unless you also apply an incremental backup which captures all changes made to your drive over time. The better incremental backups will let you apply all the changes from a specific date forward. If your whole drive gets wiped out or simply fails, you cannot recover by simply reloading all your files. It turns out that for our programs today to work, they make many changes to the operating system. Replacing the files will not apply the operating system changes so your programs will not run. A cloned backup makes an exact copy of your main drive including operating system so it can simply replace the failed drive and resume running all including any loaded programs. Just like a regular backup, you also need to have your incremental backup working or you will lose all changes since creating that clone backup. Another type of backup is called mirroring which is used on larger commercial systems, but is starting to be seen more on individual PCs. Mirroring installs a twin extra drive and special software that writes the same thing to both drives at the same time. It also has special checking to make sure you get accurate information if one of these units should suffer a complete or partial failure.
You also need to know that just because you back up religiously, does not mean that your information is safe. If your backup is with your PC and both get stolen, burned up, water damaged, etc. your backup is also gone so of no value. If you backup to the same backup disc, tape or CDs, you need to know that most computer backup media and devices can wear out and leave you with nothing. Unless magnetic floppy discs and tape are replaced regularly, the magnetic spots simply tire and evaporate within about seven years. Worse, tapes and floppy disks have read/write heads that touch the media surface causing wear on both the media and the device. You can only use the same cassette or tape so many times before the coating is so far gone that the data vanishes quickly. This short media life and high cost pretty much killed floppy discs, cassette tapes, and even VHS tapes in favor of CDs where little holes are burned in the CD disc and the read write mechanism never touches the media. Most government and large organizations have long term systems and records stored on computer tapes, so they also use regular programs to oversee tapes so they get copied onto new tapes every few years.
Like many I have two PCs, a tablet and a cell phone. All are PCs with different features and all need backed up.
For my phone I pay for cloud space and have all programed to do constant automatic backups.
For my tablet the only thing I backup is its removable pretty large additional memory chip that I added which contains my music, recipes, notes, and other stuff I tend to do on the tablet often when watching TV. I have the ability to plug two of those additional memory chips into my desktop PC (you can buy fast USB add-ons) and since this only contains data can simply copy the old to a new for my backup. My one real care in doing this is since they are tiny and look identical, I add a backup file date to the original that I check before backing up to make sure I am copying the right chip.
My laptop is similar to most new units in that it contains a solid-state disc that runs everything, plus I added a hard drive for the huge amount of data and email involved with my business and engineering activities. I use Acronis to clone the solid-state drive to a large memory chip. To do so I had to buy a fast USB connection that works with the large chip. I also clone the internal hard drive, and keep incremental backups on an external drive. This system is not ideal and has caused me some problems in the past where I ended up losing most on my portable. Fortunately, my portable is almost exclusively used when I travel and all on it except what I add during traveling is kept on my desktop computer.
My desktop gets my most thorough backup. This system has a large solid-state main drive like my laptop, but it also has a very large hard disc. It also has built-in read-write capability for large memory chips and USB drives. When I first built this system, I did not trust my solid-state drive so what I did was kept my main drive so it could do all and contained everything. That meant I had a regular schedule to clone that main drive, do full backups and kept my incremental backup program running with those backups going to an external backup drive. This was a huge system and even with a very fast processor and hard drive, I had time to go brush my teeth between the time I turned this system on and it was fully booted up and ready to work. Adding a solid-state drive reduced total bootup time to about seven seconds. Delays were similar every time I went to use another of my larger programs, so I slowly moved over most of my larger programs to my solid-state drive making these programs almost instant starting. Each program that got moved had to come off the hard drive because the operating system would only allow one identical copy of each program on my PC. Also, every time I added a new program it made changes to the operating system on the solid-state drive even if I put that program on the hard-drive. This meant I had to backup both my solid-state drive and main drive at the same time. Here are the procedures I used to backup my desktop PC.
An initial backup was something I chose to make so if I had a total system failure I would still have the software to reboot with new solid-state and hard discs to get all going again. After I loaded my operating system and applied all the latest changes, I made a full cloned copy onto a memory stick, so if my system died, I could immediately reboot from that memory stick. To make that memory stick I had to choose to use the format and make the drive bootable option. I also could do the same using Ghost, a part of the extended Symantec's Norton tool set which can also be separately purchased. I also used these same tools to make regular full backups and incremental backups to an additional drive. That additional drive is a backup drive for my portable PC and it is an additional drive in my desktop.
To backup my solid-state drive I had to power off, insert an additional blank hard drive or same sized memory chip, then use the clone software to copy over that drive. This left me with something that could be used in place of my solid-state drive if it failed. I initially thought I could do this only when I added new software, but after a little research learned there is so much else that is tracked by the operating system I needed to backup that solid-state drive just as often as my regular hard drive.
To backup my main hard disc I used my current copy Acronis True Image disc backup software to create a clone copy. This makes a 100% copy of the main drive on an additional drive. I try to do a 100% backup clone of my main drive at least quarterly and leave the incremental backup running.
There are lots of options for doing incremental backups. With the cost of drives so low today, not doing incremental backups to their own separate drive is foolish. Early on I used Microsoft task scheduler to do daily runs of a simple bat file that uses the XCOPY32 command to copy all of the main hard drive to a second drive replacing the changed files. Now my incremental backups are provided by my Symantec Norton utilities. There are other options that some experts prefer because the Symantec programs have a lot of overhead that can slow your PC. Regardless, you must do incremental backups.
Finally, I also have a special arrangement with my Internet Service Provider (ISP) who offers cloud storage to have extra storage to save key files where I can get at them from where ever I may travel. I keep my presentations, favorites, pictures and anything else I would hate to lose on cloud storage.
In addition to systems backup, I also set up my spreadsheet, word processor, presentation packages and other applications to automatically make backup files every ten minutes.
I also have slowly trained myself to do work saves every once in a while, just in case.
Not just any obvious restoration process will work. In fact, most of the various techniques shared by even the backup and recovery software providers is not safe. You not only need to learn how to do backups and do them regularly, you also need to know how to do safe restores.
I should have done a much smarter restore. What I should have done is remove all the hard drives and put in my memory stick and a new hard drive then booted and put a copy of the operating system on that new drive. To that I should have used my key to reload a new copy of the Norton programs, I have their expensive suite of all their tools multiple PC version, then gone through the updating process. After the virus checker was updated, I then should have installed the prior backup drive without trying to restore and first checked it with the virus checker. If there were no viruses found, I should have used Acronis to make a copy of that drive on a new drive. This is important, because I have learned that it often takes a few weeks before new viruses are addressed. That copy which was not left in the system meant I could later restore if there was still an existing problem. If all vanished after my restore, then it would have been time to call Norton and wend my way through the phone maze to find someone who knew what was going on. Odds were they would have already had hundreds of calls and might have a manual repair where we could delete the virus on the hard drive and in memory. Then another round of backup then follow their deletion procedure, then do a restore. Hopefully, losing all of my incremental backups since two backups prior then ran my updated virus checker against all. It found nothing but again after I left the system for about an hour the virus went off and wiped out my hard drive and second backup drive.
That image will let me quickly and totally reload my basic system with all of its specific hardware drivers. drive I keep in my system, plus make incremental backups to that same second drive. This lets me do a restore by using the memory stick to build a new system. Then what I do is load and update all of the latest virus checkers and use them on my backup drives before I risk doing a restore.
This and the Norton incremental backup will let me totally restore my system. Again, restoration of a complete wipeout has to go carefully. I assume the worst meaning the reason there was a failure was because of a virus. That image will let me quickly and totally reload my basic system with all of its specific hardware drivers.
For a program to work there are a literally thousands of pieces that all have to fall in place. Early PC software makers had to include in their programs an appropriate hardware driver for every different kind of peripheral that could be attached. This took thousands of lines of extra code that most could not use and forced vendors to spend many person years writing all these drivers and testing them in every possible configuration. Few were ever successful and it became common practice to just release new products and let the customers work out the problems, of which there were many.
The reason Bill Gates is the richest man on the planet is he was smart enough to realize the key to solving this problem was standardization. He built MS-DOS (MicroSoft - Disk Operating System) to provide a standard interface. Any hardware firm that wanted to sell a new device had to provide a standard MS DOS driver to talk with that device. As a result, software firms could get out of the device driver business and refocus on building better and better-quality programs. This quickly let the IBM PC compatible systems have by far the richest library of software that was the most reliable, easiest to use, and far less expensive. Customers were more than willing to pay less for a better product. Within five years Microsoft owned the whole PC market and these tools were easy enough for almost all to use, so the PC market exploded from a few thousand to hundreds of millions.
As the PC industry matured, new hardware also had to come with special software drivers or "applets" to support things like playing music, showing pictures, allowing animation, etc. A rich set of these software drivers cuts the overhead to build a new program by as much as 80%. Other PC software makers could either adopt the same standard, or spend far more and much longer to produce a product that will not be cost competitive. Almost all joined forces using the same standards.
Microsoft has made using these standards relatively easy, but still leaves new software creators in a bind. The competition for the billions of dollars PC customers spend is far beyond fierce. Any software product that comes out too late to capture market share rarely is successful. Likewise, any company whose programs get a reputation for not working, often suffers an early demise. With competition so fierce and time to market so critical, vendors must use the latest software drivers. Vendors know that most customers don't have a clue as to what is meant by driver, let alone that there is a difference between hardware and software drivers. Their solution is to install the latest set of standard drivers automatically when loading their new program. They do so without either asking or telling you. After all, the average PC user only wants the $#@*&^ thing to work.
Although this is great if you are loading a new program, it makes for big problems when you are loading an old program. That same favorite game or program that has always worked perfectly before, suddenly becomes your worst nightmare three years later. Most, including me, get caught by an old program. Often there is no clue as to what happened or even when, let alone what you are going to have to do to make repair. All most see is that suddenly one or more things that have always worked before either run terribly or not at all.
Finding the problem is near impossible, even if your problem occurs during loading the offending program. It is difficult to distrust your favorite program that has always loaded and worked perfectly in the past. I have seen more than one PC store make hay out of this dilemma convincing the customer it is a serious hardware problem requiring major upgrade, system replacement, or expensive full software reload forcing you to start all over. None is attractive.
Most PCs I see have older versions of software drivers for almost all of their sound, video and even CD ROM functions. A few out of date drivers just will not work at all. Even Microsoft is unwilling to admit how rapidly these software drivers change. They do not want their customers in the business, nor should customers be in this business of doing software driver updates. The Microsoft solution starting with Win95B is a warning message that an older file is trying to replace a newer. Your response should be to never allow an older file to replace a newer. Win95, in spite of all its bad press, is an incredibly good program and keeps itself running by going back to the original generic drivers which work on most everything but are real slow.
Simply loading your software from oldest to newest, will self-cure most of these problems but not all. On the system that inspired me to put up this page I ended up having to reload Win95, reload the four major patches released by Microsoft, then load up my latest Microsoft multimedia CD ROMs to fix the software drivers.
Error files mostly come from doing improper shut down of your PC or removing drives and thumb drives improperly. The only way to avoid error files being created during turning off your PC or removing drives is to always use the Eject Shut Down buttons. The reason for this is part of how your PC works. Windows tries to run all from memory to optimize performance because memory is thousands of times faster than hard disk. Unfortunately, there is not enough memory, so your PC stores part of each file in use in memory with the rest of the file on hard disk. Just pulling a drive, turning power off, pressing the reset button, or rebooting, instantly clobbers the memory portion of the file in use and leaves an incomplete file piece on disk.
These incomplete pieces are found on your next startup when your system checks its file directories. It asks to run ScanDisk that will turn those file pieces into files. The corrected error files created by Scan Disk are stored in C:\ known as the root directory and are named "FILEXXXX.CHK" where XXXX is a sequential number. The good news is that Win95 only runs from copies of program files, so all you may lose is the working copies of your data or document that you were working upon. Most of these FILEXXXX.CHK can be erased with no problem. Never bypass a system request upon startup to run Scan Disk or your file problems will rapidly compound. I setup my scheduler to run a full Symantec Disk Doctor (or Windows SCANDISK) once a month.
Most PCs that I see from friends with poor performance suffer from having huge numbers of temporary files, lots of saved files in their trashcans, and from a failure to do regular disk defragging. Realize that the different versions of the Microsoft Windows operating system each do a full directory scan on startup, so the more file and pieces of files you have on your PC, the slower it will start.
Your PC will build up all kinds of extra files just doing normal things. The extra files include many Recycle, Temp, and Temporary Internet Files. The c:\windows\temp folder is where many programs put temporary files used during loading new programs and uncompressing files. The files in this directory need cleaned out depending upon how much software you are loading. Additionally, the way that both MS Internet Explorer and Netscape browsers work is they save in temporary areas work files for every site, file, picture, piece of music, and all else you see or hear from the Internet. These all land in the c:\windows\temporary internet files folder and subfolders under that folder. They also save the addresses of each site you visit in the c:\windows\history and the c:\windows\recent folders. There are a few files that can not be erased and must be ignored, but all else needs cleaned out regularly.
These folders must be regularly cleaned out. The good news is newer Windows programs automatically delete most of this garbage unless you till them not to. I also clean out the directory as it contains the addresses of any files or pics that I have looked at on the net recently. Some of the sites my well intentioned friends share contain pictures and content not suitable for my kids. *blush*
A closely related problem is PC lockup during use of the Internet. To keep rapid access to all you have visited during an Internet session, your PC keeps all these files, pictures, and text as open files, each taking both hard disk and a tiny piece of memory. In as little as two hours of heavy surfing or visiting in a chat room you can fill your PC memory and cause your PC to lock up. The fix is to watch system performance and when it lags, you proactively do a system restart and file cleaning instead of crashing.
Some people also recommend cleaning out the c:\windows\cookies subdirectory, I did for a while, but found these files were taking no real space, and without them, I had trouble logging into places like MS and Symantec for my software updates. These cookies are used for identification and I quickly tired of having to fill out a mess of forms before being able to download updates.
I have also found that when my history file grows real large, my system startup is slower than molasses. I think, that what is happening is that the start-up is going through these addresses in expectation of firing up the Internet. Again, using more current versions of Windows automatically takes care of this problem.
I do my erasing by going into the desired directory then using the EDIT command from the top menu bar to select all files, followed by using delete from the FILE command. You can also clean out the Internet History File directory from within MS Internet Explorer by selecting View, Options, Navigation, then selecting clear history.
After you delete all this stuff it is still not gone! You then need to go into your main page and empty the recycle bin using a right mouse click. Regularly emptying the recycle bin is needed or it quickly gets huge.
Cleaning out all this stuff is a pain, so I wrote a quick bat file to do the work for me on startup. You can also put it into the autoexec.bat to make it run on startup every time your PC is turned on. Or you can put it in the root and execute it with a Start then run. It will not have access to any open folders, so running in Autoexec.bat is better. Regardless of where you put it will have to answer Y to each of the are you sure on the delete/erase questions. This is what I use:
C: CD \
CD C:\WINDOWS\TEMP
ERASE *.*
CD C:\WINDOWS\HISTORY
ERASE *.*
CD C:\WINDOWS\RECENT
ERASE *.*
CD \
DELTREE C:\WINDOWS\TEMPOR~1
EXIT
You can also add the RECYCLE folder to this list, but if you do, you lose the ability to recover files after you turn off your PC. I choose not to have it in my bat file and still clear my recycle bin by hand every week or so. It has saved me more than once!
You also need to realize that all these little file pieces use up parts of your hard drive, then when they are erased they leave little empty spaces. Windows likes to have enough room to write a whole file at once. Writing in pieces is very slow and can quickly wear out a hard drive. Windows comes with a utility knows as defrag to address this problem of consolidating space. You run it by selecting Start, Programs, Applications, System Tools, the Defrag. I recommend you do a defrag at least once a month. Moreover, I also recommend you add more hard disk drives whenever you need to. Many say when your drive gets more than half full it is time to go to twice as large a drive. As I update this comment, I recall sitting with two of my very expert friends and the three of us were bragging that we each had dual 10 mega-byte hard drives and were certain there was no way we would ever need more disc. I now have individual pictures that use more than 10 MB. Do not do defragging on solid-state drives as it can quickly ruin them and is not necessary!
Many of today's programs ask you if they may automatically start. You should always say no! If you do not, you will soon have so much running and filling your limited memory, that your system performance will either be really slow or just plain die altogether. A single ctrl alt delete will show you all the programs you are running at any given time. Just after startup before you run anything else, there should only be about six or seven, all from Win95 and perhaps from Symantec or a screen saver. If you have many more than this there is a problem.
These auto start files are launched from the c:\windows\startup\programs\start files directory and any scheduler you have running plus from the WIN.INI, WINDOWS.INI, SYSTEM.INI, and windows registry files. It is easy to delete the programs from that start up folder and your scheduler, but finding the others can often stump the experts. This is why you should always say no, as it is easy for you to add what you want into the startup folder later.
Spyware is a special class of programs that automatically start. Vendors slip spyware onto our PCs when we visit certain Internet sites, when we load many different programs both free and commercial, and when we get certain emails. The early spyware was limited to cookies that kept a little information so that when we revisited a web page we did not have to enter a bunch of stuff again. More current spyware sits quietly using almost no resources to track our behavior, what web pages we visit, and what email advertisements we open so vendors can better target their advertising campaigns to increase their chances of reaching us with something we will look at. Unfortunately, many vendors of spyware have gotten completely out of line and a few of the unscrupulous have modified spyware to track our every keystroke to enable them to steal passwords, credit cards, etc. It was at one time near impossible to even find out if spyware was running on our PCs. Lavasoft came out with AdAware that runs and finds sneaky spyware and lets you delete if from your PC. Spybot did a far better job and permits you to find, remove, and block discovered spyware programs. Click here to get a free (donation requested) version of Spybot. I setup my Spybot program to constantly monitor and do a full scan weekly.
SPAM is the term used to describe the untold volumes of garbage email that comes unsolicited from vendors in droves. If you don't regularly clean this junk out of your inbox and deleted files mail boxes, it will quickly overwhelm your PC causing it to slow markedly and to rapidly run out of available disk space. Some SPAM email is actually a way for unscrupulous individuals and vendors to slip spyware onto our machines or to spread viruses. There are a number of new SPAM programs being developed, but the state of the art is at best still deplorable. Often using a SPAM killer takes longer and is more trouble than just deleting the emails ourselves.
If you use Microsoft Outlook Express, you can actually block the folks that hit you most often. This is not too hard, but does take a little work, and understanding what is going on helps a bunch in your blocking efforts.
Most Internet Service Providers (ISPs) who host our web pages and that we use with either a modem, DSL, or cable connection to access the Internet hate SPAM senders even more than we do. SPAM ties up their limited resources, storage, and greatly slows down performance for their customers. As a result, most ISPs actively get rid of any customer who uses their servers to send SPAM. To keep from losing their Internet connections, many who do advertising by email have turned to some pretty nasty ploys. They use hacker software to trick other people's computers and servers to do the mail sending while they stay anonymous.
Each email sender has a name that we can read in English, and they have what is called their IP that is short for their Internet Protocol ID. The IP is made up of four groups of numbers, each up to three numbers long, separated by periods. It is pretty easy to block or change the name used to actually send you an email, but your email program will not accept any email unless it is coming from a valid IP address. That IP may not be the person who sends you the email, but instead the ISP server that the email sender tricked into sending you the mail. Most reputable ISPs have long since put up firewalls and other tools to keep their systems from being misused to send garbage emails. That means that the odds are near 100% that the IP that sends you a piece of garbage email, SPAM in other words, is one you can safely block
Microsoft Outlook Express mail program lets you automatically send to the delete box an individual, group, or specific IP address. I found blocking an individual by name did no good at all as SPAM senders change names with every mailing. Blocking a group such as "AOL.com" cost me too many friends. But, blocking an IP really works well as there are not that many servers being misused to send all the SPAM. In a week of diligent and somewhat hard work, I reduced my number of SPAM emails from over a hundred a day in my inbox to less than a dozen. To do so:
Start by right clicking on an offensive email in your inbox, then selecting properties, then pick the detail tab. Now paint with your mouse and copy the from IP address that is usually at the end of the second or third line (don't copy your own IP!).
Close that properties window and go to Tools, Message Rules, Blocked sender's list, and select Add. Do a paste of the IP you got in the prior step making sure you delete off any spaces or the [] square brackets that surround that IP in the properties. Click Ok and then OK again to close that window.
That's all there really is to it, and as awkward as seems, after the first few hundred, you will find yourself only doing a few of these a day. All that garbage email ends up in my delete folder. I scan it briefly and wipe it out. In a few cases I put an IP that I really did want to see email from, and just went back and deleted it from that list of blocked IPs.
Even with all the best care in the world you may need to rebuild your system due to a virus, dead hard drive, or even getting badly hacked when surfing the net.
Most of the time I have been able to do a recovery by reloading Windows over the top of the prior copy. Sometime, even this will not work and you have to go all the way back clearing the hard drive with FISK, FORMAT, and reload from scratch.
If I was brilliant, my backups already include a Symantec Ghost image of my basic hard drive making a reload easy. All I need to do is insert my boot floppy and the Ghost CD I made.
When I am remiss or end up helping a friend who did not do that, I first try to do a simple restore of Windows. Just put in the original Windows CD and click on setup selecting ALL standard options. (the only exception is the modem communications stuff) After the Windows reloads there are additional things which you need to do.
I then update my motherboard drivers following the instructions from either their provided disk or more than likely updates from their web site.
I always then go to the www.Microsoft.com web page and run their update check to ensure all the latest service packs and updates are loaded on my PC. One of the options on that page that I always enable is to have my PC automatically regularly check to see if there are any needed updates. Without these updates, the PC is wide open to viruses and other attacks. After running some of the patch files you must restart your PC before running the next patch. Clearly frustrating, but still far better than having my system clobbered
I then reload my custom drivers and/or MS Internet Explorer that may have been trashed. I am finding that about every three or four months I have to reload MS IE and about every six or so months Win95. The reason is not because these products are unstable, but because I get hacked or whacked by someone from the Internet that screws up settings I cannot otherwise change back.
![]() Feel free to email me with pictures, music, comments, suggestions, etc!
Feel free to email me with pictures, music, comments, suggestions, etc!
Credits:

